The European Union's Cyber Resilience Act (CRA) is imposing firm deadlines on manufacturers of connected building products. Mandatory incident reporting obligations take effect on 11 September 2026 - more than a year before the regulation's full enforcement date - leaving vendors of smart HVAC controllers, access readers, energy meters, and building management system (BMS) gateways with far less preparation time than many assumed.
Background
The CRA entered into force on 10 December 2024, according to the European Commission, establishing a phased compliance timeline that culminates in full enforcement on 11 December 2027. The regulation applies to any product with digital elements - encompassing hardware, software, and remote data processing solutions - placed on the EU market. For the building sector, this captures the broad IoT device ecosystem embedded in commercial facilities: connected sensors, wireless lighting nodes, IP-enabled fire panels, edge gateways, and BMS integration platforms.
Unlike earlier EU directives focused on the network and information systems of organizations, the CRA targets the security of products themselves. According to the European Commission, the regulation aims to ensure that IoT products and connected devices are made secure throughout the supply chain and throughout their lifecycle. This represents a structural shift for building technology vendors accustomed to releasing products under market-driven security practices rather than legally mandated ones.
The regulation builds on the 2020 EU Cybersecurity Strategy and complements the NIS2 Directive, which already extends cybersecurity requirements to building automation systems supporting essential services. Where NIS2 addresses the obligations of building operators, the CRA directly governs the devices those operators procure.
Key Requirements
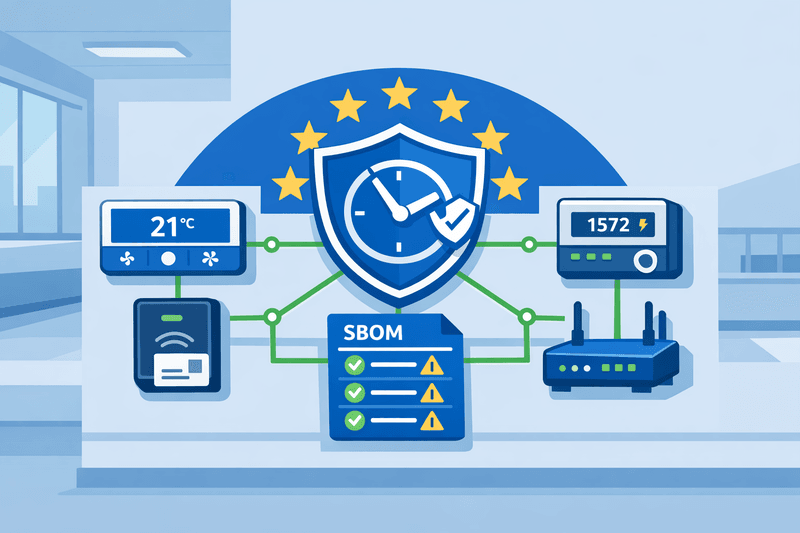
The CRA establishes three primary obligations for manufacturers. First, security by design and by default: according to the legislation, manufacturers must embed cybersecurity into products from the initial design phase, with secure default configurations, strong authentication, encrypted communications, secure boot, and automatic security update mechanisms. Second, vulnerability management: manufacturers must continuously monitor all product components for vulnerabilities and issue timely patches, including for third-party and open-source software embedded in their devices. Third, incident reporting: from 11 September 2026, manufacturers must report actively exploited vulnerabilities to ENISA - the EU Agency for Cybersecurity - and designated national Computer Security Incident Response Teams (CSIRTs) within 24 hours of discovery, per the European Commission's official implementation timeline.
Critically, the reporting obligation applies to all products already on the EU market, including those placed there before 11 December 2027. A legacy IoT gateway installed in a commercial building in 2019 remains subject to the 24-hour reporting rule if an active exploit is discovered after September 2026.
The CRA also mandates Software Bills of Materials (SBOMs) for all covered products, giving regulators and customers a full inventory of software components. While SBOMs do not become formally enforceable until December 2027, legal analysts note that SBOM readiness is a practical prerequisite for meeting the September 2026 reporting obligation - manufacturers cannot report on a vulnerability they cannot trace to a specific component.
Non-compliance carries significant consequences. Under the regulation's penalty framework, manufacturers face fines of up to €15 million or 2.5% of global annual turnover, whichever is higher. Products without a valid CE mark demonstrating CRA conformity cannot be placed or retained on the EU market.
Outlook
The European Commission published draft guidance for stakeholder feedback in March 2026, and harmonized CRA standards are expected from Q3 2026 onward, providing manufacturers with clearer conformity assessment pathways. However, the absence of finalized harmonized standards remains a source of uncertainty, with many product teams building toward requirements still being defined at the technical level.
For system integrators and building operators, vendor compliance posture is becoming a project specification variable. Procurement teams will increasingly need to verify SBOM availability, update lifecycle commitments, and vulnerability disclosure policies before specifying IoT devices for commercial deployments. Vendors that demonstrate CRA readiness ahead of the December 2027 deadline stand to gain a procurement advantage in specification-led markets across the EU.