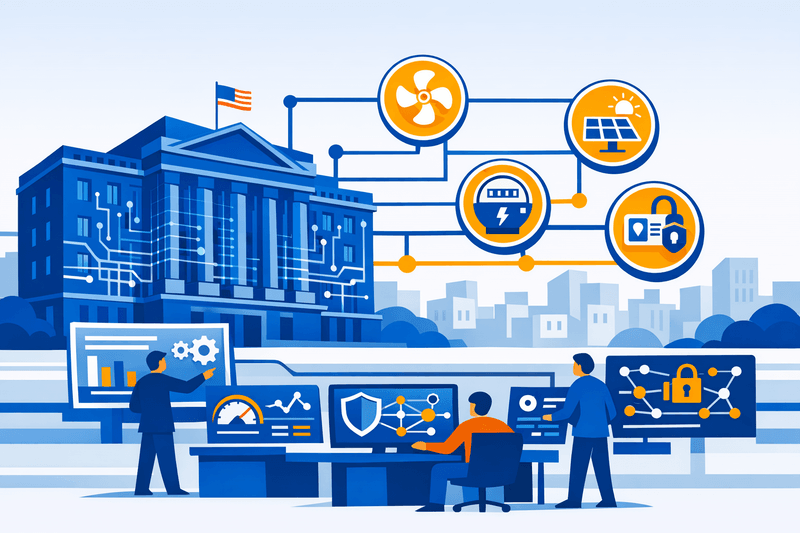
The U.S. General Services Administration's (GSA) smart building pilot at the Oklahoma City (OKC) Federal Building now serves as the operational template for building automation system (BAS) interoperability standards and operational technology (OT) cybersecurity requirements across the federal real estate portfolio. Completed in May 2023 and subject to renewed Department of Energy (DOE) scrutiny in 2025, the project is directly shaping updated procurement language and technical reference standards that private-sector contractors and system integrators must meet to compete for federal work.
Background
The OKC Federal Building renovation was executed as a grid-interactive efficient building (GEB) project under a utility energy service contract (UESC) with Oklahoma Gas & Electric (OG&E), with energy service company Ameresco as the prime contractor, encompassing the Oklahoma City facility and four additional Oklahoma federal buildings. Funding totaled approximately $11 million, drawn from a DOE grant and GSA appropriations. The National Renewable Energy Laboratory (NREL) provided technical engineering support, including lifecycle cost and energy optimization analysis via its REopt platform.
The project emerged as GSA's Public Buildings Service (PBS) was formalizing its Smart Buildings program directive - a policy framework requiring all federally owned buildings under GSA's jurisdiction to adopt consistent controls across building automation, energy management, physical access, and cybersecurity systems. That directive explicitly mandates promotion of interoperability between devices through open protocol systems, with the objective of converging normalized data on at minimum a facility-wide tool, and requires implementation and maintenance of cybersecurity best practices for all IP network-based systems, including downstream devices.
Details
The OKC project team implemented nine energy conservation measures (ECMs) and smart building technologies, including solar photovoltaic arrays, battery energy storage, new HVAC controls, and LED lighting retrofits. The project is projected to reduce building energy use by 41%, cut approximately 3,100 metric tons of carbon emissions annually, and save around $400,000 per year in energy and water costs.
Integrating the varied control systems proved a central challenge. According to the DOE Federal Energy Management Program (FEMP) case study, existing and new equipment used a variety of control systems, which proved challenging from a coordination and integration standpoint - a friction point the pilot team identified as directly informing updated procurement specification language for future deployments.
On cybersecurity, GSA's Building Technologies Technical Reference Guide (BTTRG) Version 3.0, published in May 2024, now governs how BAS, advanced metering systems (AMS), lighting control systems (LCS), and physical access control systems (PACS) are deployed across the federal portfolio. The guide requires that building management and control (BMC) systems obtain a FISMA Moderate Authority to Operate (ATO) and aligns IoT device security with NIST Special Publication 800-213A, the IoT Device Cybersecurity Requirement Catalog. The OT-specific security layer references NIST SP 800-82 Revision 3, the Guide to Operational Technology Security, published in September 2023. GSA's overarching cybersecurity policy also mandates inclusion of cyber supply chain risk management (C-SCRM) principles, in accordance with NIST SP 800-161, across all building control system procurements.
Analysts note a structural gap in existing federal contract clauses: FAR clause 52.204-21, which mandates 15 basic security controls derived from NIST SP 800-171, is designed for IT systems and is not directly suited to OT that monitors and controls physical building functions. The OKC pilot's documented integration challenges are cited by GSA stakeholders as justification for developing OT-specific procurement templates to close this gap in future solicitations.
ICS-CERT alerts involving building automation systems have risen steadily for five consecutive years, and industry researchers report a 30% year-over-year increase in OT-specific cyberattacks. These threat trends reinforce the urgency of GSA's push to embed OT security baselines directly into BAS acquisition requirements before cross-agency rollout.
Outlook
GSA has signaled intent to replicate the OKC model across its portfolio of more than 370 million rentable square feet of federally owned and leased property. For private-sector contractors and system integrators, the pilot's lessons translate into enforceable procurement requirements: open-protocol BAS architecture, FISMA-aligned ATOs for all networked building control systems, and demonstrated C-SCRM compliance throughout the equipment supply chain. Firms lacking established OT cybersecurity documentation and interoperability certification will face growing barriers to qualification on GSA building contracts as standards derived from the Oklahoma City experience are embedded into updated solicitation templates government-wide.