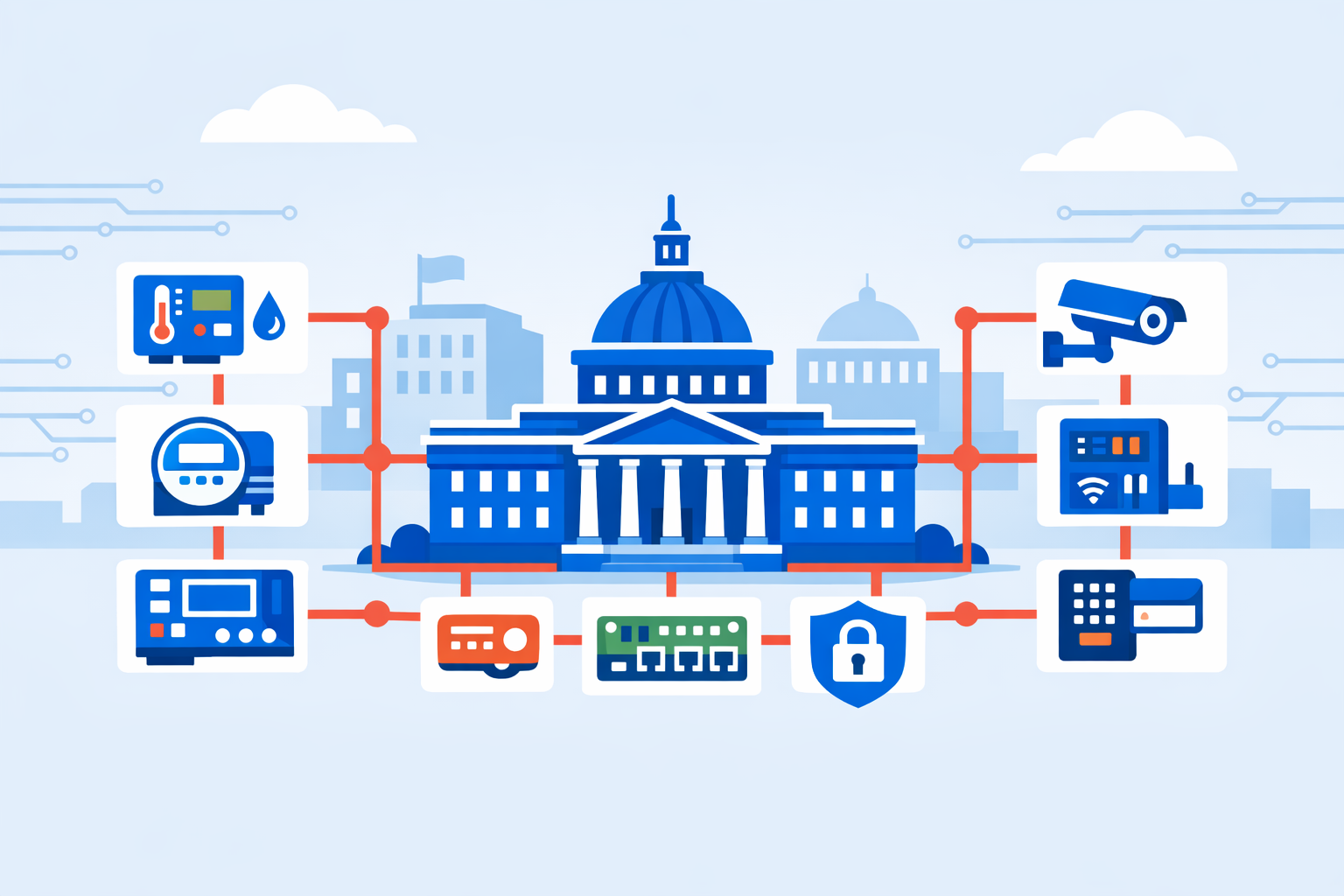
The conclusion of the U.S. Department of Energy's Federal Smart Buildings Accelerator (FSBA) and the subsequent wave of agency-level smart building investments are driving substantive changes to federal procurement frameworks, interoperability requirements, and operational technology (OT) cybersecurity obligations - with implications that extend directly to private-sector integrators and building automation system (BAS) vendors.
Background
In alignment with the Energy Act of 2020, the U.S. Department of Energy's Federal Energy Management Program (FEMP) launched the Federal Smart Buildings Accelerator to promote the adoption of smart building and grid-interactive efficient building (GEB) technologies across federal facilities. The FSBA was introduced at Energy Exchange 2022 and concluded in September 2024.[1] Its reach extended to facilities operated by the General Services Administration (GSA) and the Department of Veterans Affairs, among others.
In parallel, the GSA announced plans to invest $80 million from the Inflation Reduction Act in smart building technologies, targeting an estimated 560 federal buildings across 49 states, Puerto Rico, the U.S. Virgin Islands, and Washington, D.C. The $80 million is part of a broader $975 million allocation to the GSA for emerging and sustainable technologies and related sustainability programs. The scope of these investments has placed procurement practices, data infrastructure, and cybersecurity governance under renewed scrutiny.
Details
The FSBA's technical assistance across federal facilities revealed several structural constraints. The accelerator promoted smart building and grid-interactive technologies, uncovering strong interest but persistent challenges with funding and implementation. Many agencies lack the staffing and time needed for GEB technology adoption, and limited maintenance budgets hinder significant equipment upgrades that could deliver measurable efficiency gains.
On the procurement side, federal implementation of data-integrated building systems has lagged due to procurement guidelines that favor standalone systems, risk aversion in the contracting chain, and cybersecurity concerns - compounded by the absence of interoperability standards and systems specification guidance. GSA's smart buildings directive now formally addresses this gap: the policy directs facilities to promote interoperability between devices through open protocol systems, implement and maintain cybersecurity best practices within IP network-based systems including downstream devices, and protect against threats through the inclusion of cyber supply chain risk management (C-SCRM) principles.
On open standards, industry consensus is converging around a common set of protocols. BACnet remains one of the most widely used building automation protocols worldwide, developed by ASHRAE in the 1990s as an open standard and sustained by innovations such as Secure Connect and ISO standardization. Alongside communication protocols, common data models and ontologies are equally important; key frameworks like Brick Schema, Project Haystack, and RealEstateCore are collaborating via ASHRAE 223P and other liaisons to enhance interoperability.
OT cybersecurity obligations for BAS environments are tightening at the federal level. On December 11, 2025, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) released its Cybersecurity Performance Goals 2.0 (CPG 2.0), an update to its core set of recommended cybersecurity practices for critical infrastructure owners and operators. A key structural change: OT and IT goals are now consolidated into universal goals, eliminating silos across IT, Internet of Things (IoT), and OT environments. CPG 2.0 also introduces goals addressing risks from third-party providers with deep system access and zero-trust principles to mitigate lateral movement.
Regulatory pressure is compounded by rising cyberattacks on operational technology, with Dragos reporting a 30% increase in OT-specific cyberattacks year over year. CISA and its partners have warned that cyber threat actors targeting OT components focus on specific OT products rather than specific organizations, and that many OT products lack secure-by-design principles - commonly exhibiting weaknesses such as weak authentication, limited logging, insecure default settings, and insecure legacy protocols.
Outlook
GSA's OneGov Strategy is set to expand into hardware, platforms, infrastructure, and cybersecurity services - a trajectory that positions centralized procurement frameworks to increasingly shape how BAS and smart building technologies are specified and awarded across civilian federal facilities. As federal facilities adopt automation and connect to the internet, converging operational technology and information technology, vendors and integrators operating in the federal space will need to demonstrate alignment with CISA CPG 2.0, NIST CSF 2.0, and open protocol requirements as baseline conditions of participation rather than differentiating attributes.